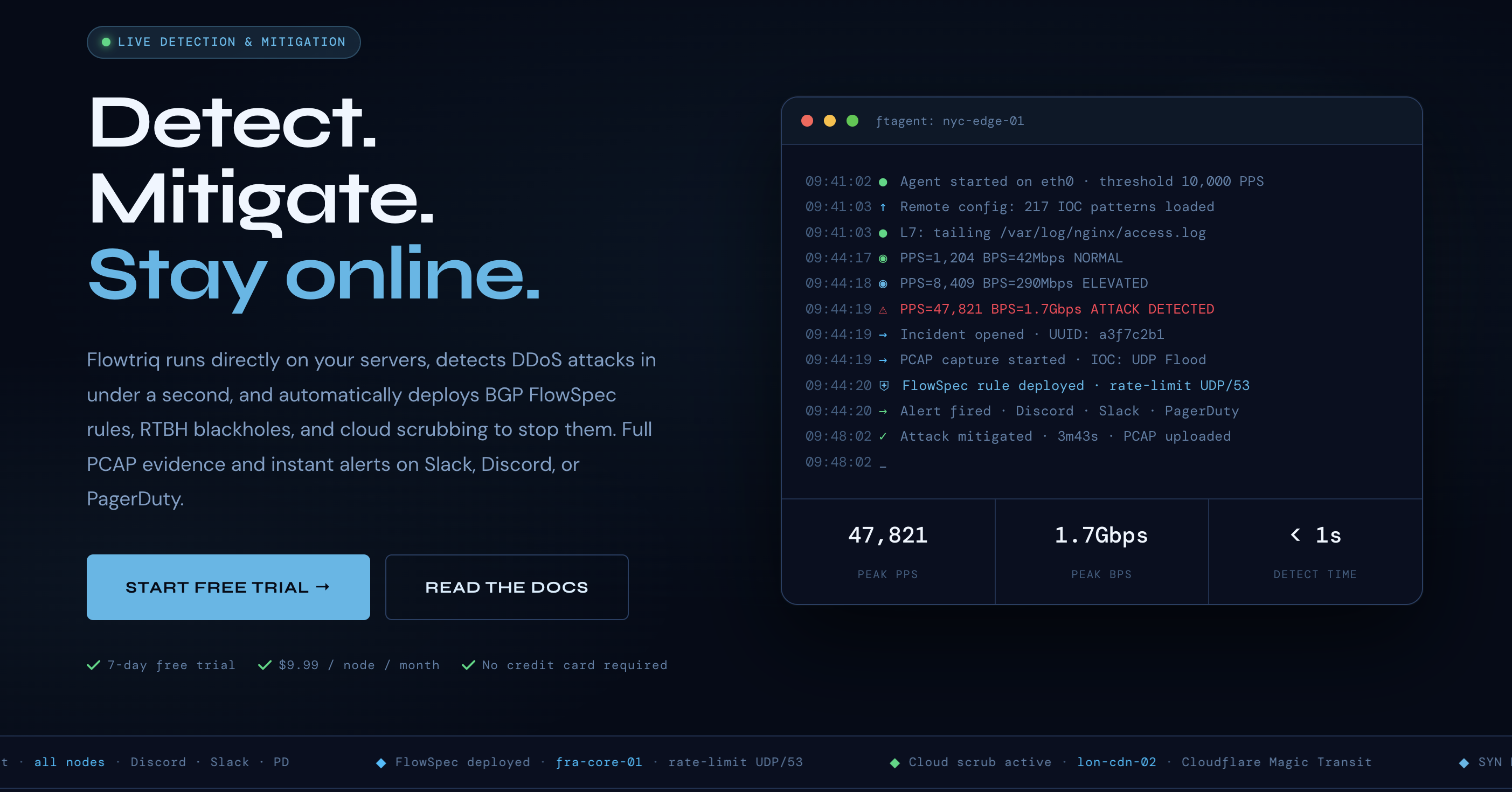
Flowtriq: Empowering Developer Tools with Sub-Second Automated DDoS Mitigation
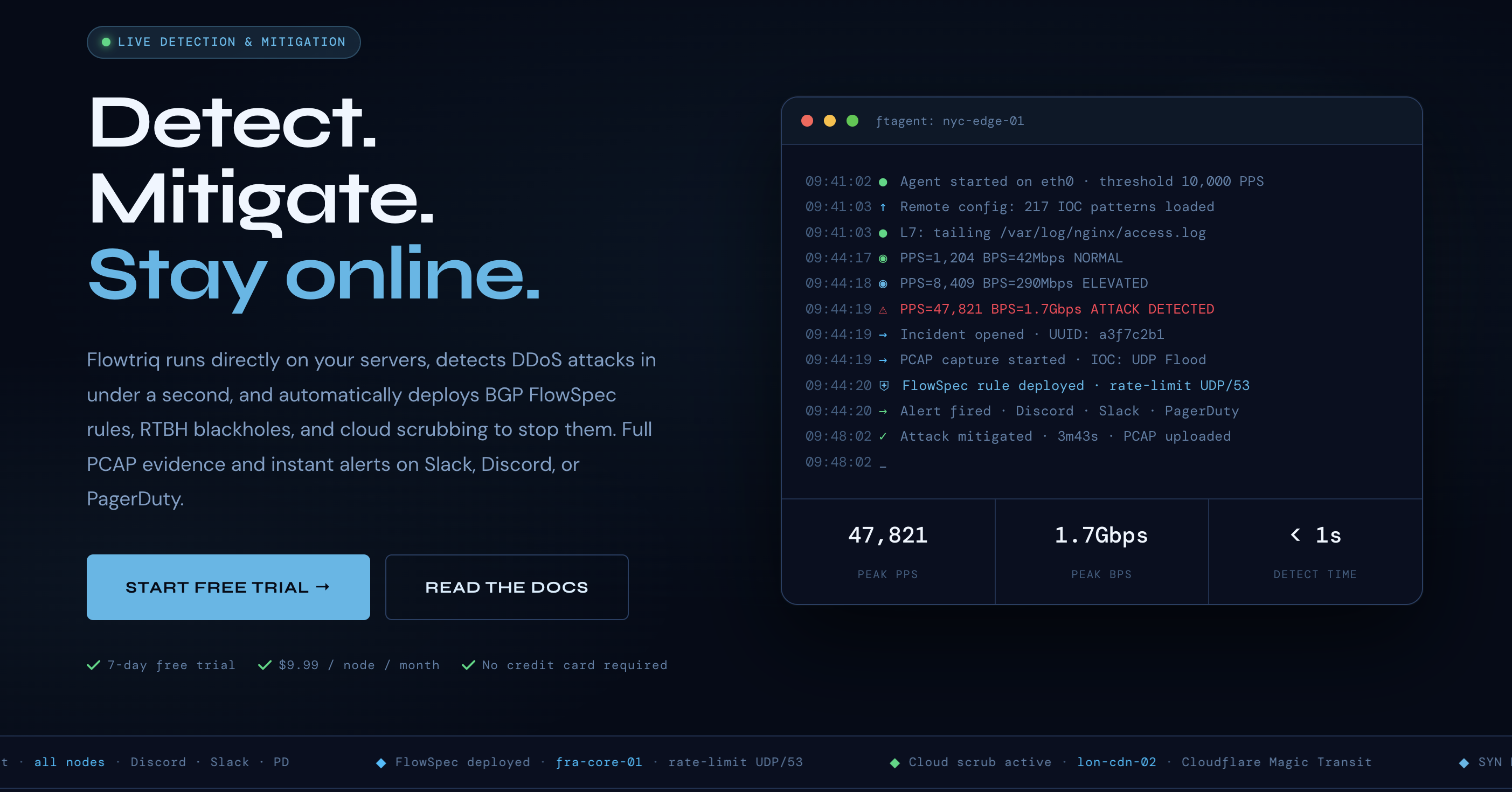
The Sub-Second Shield: Why Your Infrastructure Can’t Wait for Human Intervention
Picture this: your engineering team is finally making headway on that critical Q3 release when a "minor latency spike" hits your Slack. Within sixty seconds, that spike becomes a total blackout, your support desk is drowning in tickets, and your DevOps lead is frantically digging through logs while your burn rate hits the stratosphere. Flowtriq is the antidote to this chaos—a lightweight, agent-based DDoS detection and auto-mitigation platform that moves faster than a human can blink. By automating the transition from detection to mitigation in under one second, it transforms a potential PR nightmare into a non-event, ensuring your services stay online and your team stays focused on building, not firefighting.
The Business Case for Automated Resilience
In the current "Developer Tools" landscape, uptime isn't just a metric; it’s your brand’s heartbeat. When you’re running a SaaS platform or a game server, even five minutes of downtime can result in permanent churn. The traditional approach—hiring a 24/7 SOC or paying exorbitant "clean pipe" surcharges—is a legacy drain on margins.
Flowtriq’s market positioning is disruptive because it democratizes high-end network security. By utilizing a Python-based agent (ftagent) that learns traffic baselines autonomously, it eliminates the "tuning tax"—the endless hours engineers spend adjusting thresholds to avoid false positives. For leadership, the ROI is twofold: you’re drastically reducing the Mean Time to Remediate (MTTR) while simultaneously lowering your total cost of ownership (TCO). At a flat $9.99 per node, Flowtriq removes the unpredictable "traffic tax" often found in cloud-native protection suites. This allows for predictable financial modeling as you scale your infrastructure, providing a competitive edge against incumbents who are still passing high bandwidth costs down to the end user. In my experience, the best tools are the ones you forget are even running until you see the "Attack Blocked" notification in your morning digest.
Key Strategic Benefits
- Operational Efficiency: Flowtriq removes the manual labor from incident response by deploying automated runbooks that chain mitigation steps—like BGP FlowSpec rules or RTBH blackholes—instantly. This allows your skeleton crew to manage a massive node footprint without needing a dedicated security analyst for every ten servers.
- Cost Impact: The flat-rate pricing model is a game-changer for margin-heavy businesses like MSPs and hosting providers. By preventing "bill shock" from traffic surges and eliminating per-alert fees, you can protect your entire Resource Index without ballooning your OpEx.
- Scalability: The platform’s multi-node management and sub-two-minute installation mean security isn't a bottleneck for growth. Whether you are adding ten nodes or five hundred, the "learn-and-protect" cycle remains consistent, ensuring your security posture doesn't dilute as your infrastructure expands.
- Risk Factors: While the automation is top-tier, leadership must ensure that escalation policies are correctly mapped to their specific network topology. Relying solely on automated BGP changes requires high confidence in your upstream provider's compatibility with FlowSpec or Cloudflare Magic Transit integrations.
Implementation Considerations
Deploying Flowtriq isn't a "six-month transformation project"—it’s a Tuesday afternoon task. Because the ftagent is a lightweight Linux-based agent, the initial Resource Indexing and installation take less than two minutes per node. The real strategic work lies in the configuration of the "Attack Profiles" and mitigation playbooks.
Leadership should phase the rollout: start with a 7-day trial on non-critical edge nodes to let the dynamic baseline learning calibrate to your specific traffic patterns (like those pesky Mirai botnet variants I’ve dealt with in the past). Integration with your existing stack is streamlined via webhooks for Slack, PagerDuty, or OpsGenie, ensuring your current alerting workflow remains intact. The most significant "change management" hurdle will be trusting the automation; I recommend starting with "Detection Only" mode for 48 hours to validate the accuracy of the sub-second classification before toggling the auto-mitigation "Kill Switch."
Competitive Landscape
Flowtriq enters a crowded Tool Registry, but its focus on "sub-second" edge-level detection sets it apart from traditional cloud scrubbing services. While Cloudflare offers massive global capacity, it can often be a "black box" regarding specific packet-level forensics unless you're on an Enterprise tier. Similarly, Akamai provides robust protection but at a price point that is often prohibitive for mid-market SaaS or independent game studios.
Compared to AWS Shield, Flowtriq offers more granular control for multi-cloud or hybrid environments, especially for providers using OVH or Hetzner who need a unified dashboard. For those looking for a deeper dive into how these stack up, our "No-Code Ledger" Tool Registry frequently updates our DDoS Mitigation Comparisons to reflect real-world performance.
Recommendation
Stop treating DDoS protection as a reactive "insurance policy" and start viewing it as a core component of your Tool Registry. My advice? Sign up for the 7-day trial, deploy the agent to a single staging node, and trigger a simulated load test. If your current stack can't detect and mitigate that hit in under a second, you're leaving your uptime to chance. Move Flowtriq into your standard server image (AMI/Cloud-init) and bake resilience directly into your deployment pipeline.
Interested in Flowtriq?
Visit Website